In a world where data breaches and password leaks dominate headlines, protecting your online accounts has never been more critical. Passwords alone are no longer enough. Cybercriminals use phishing scams, malware, and brute-force attacks to compromise even the most carefully crafted credentials. This is where Twoku Authenticator steps in, adding an essential extra layer of protection that significantly enhances your online security.
TLDR: Twoku Authenticator strengthens your online security by adding a second layer of verification to your logins. Instead of relying solely on passwords, it generates time-sensitive codes that prevent unauthorized access—even if your password is stolen. It’s simple to set up, easy to use, and dramatically reduces the risk of hacked accounts. If you value your digital privacy, enabling Twoku Authenticator is one of the smartest security moves you can make.
Why Passwords Alone Are No Longer Safe
For years, passwords were considered the primary line of defense online. However, modern hacking methods have exposed serious weaknesses in password-only authentication systems. Even strong passwords can be:
- Phished through fake emails and fraudulent login pages
- Leaked in large-scale data breaches
- Guessed using brute-force software
- Reused across multiple accounts, increasing vulnerability
When one password is compromised, attackers often gain access to several accounts. This domino effect can lead to identity theft, financial loss, and severe privacy violations.
The solution? Two-factor authentication (2FA), and specifically, a reliable app like Twoku Authenticator.
What Is Twoku Authenticator?
Twoku Authenticator is a two-factor authentication app designed to provide an additional security layer during login. Instead of relying on just your password, Twoku generates a unique, time-sensitive verification code that you must enter along with your credentials.
This means that even if someone steals your password, they still cannot access your account without the second verification code generated by your device.
Each generated code typically expires within 30 seconds, making it nearly impossible for attackers to intercept and reuse it.
How Twoku Authenticator Works
The app uses Time-Based One-Time Password (TOTP) technology. Here’s how the process works step-by-step:
- You enable two-factor authentication on a supported website.
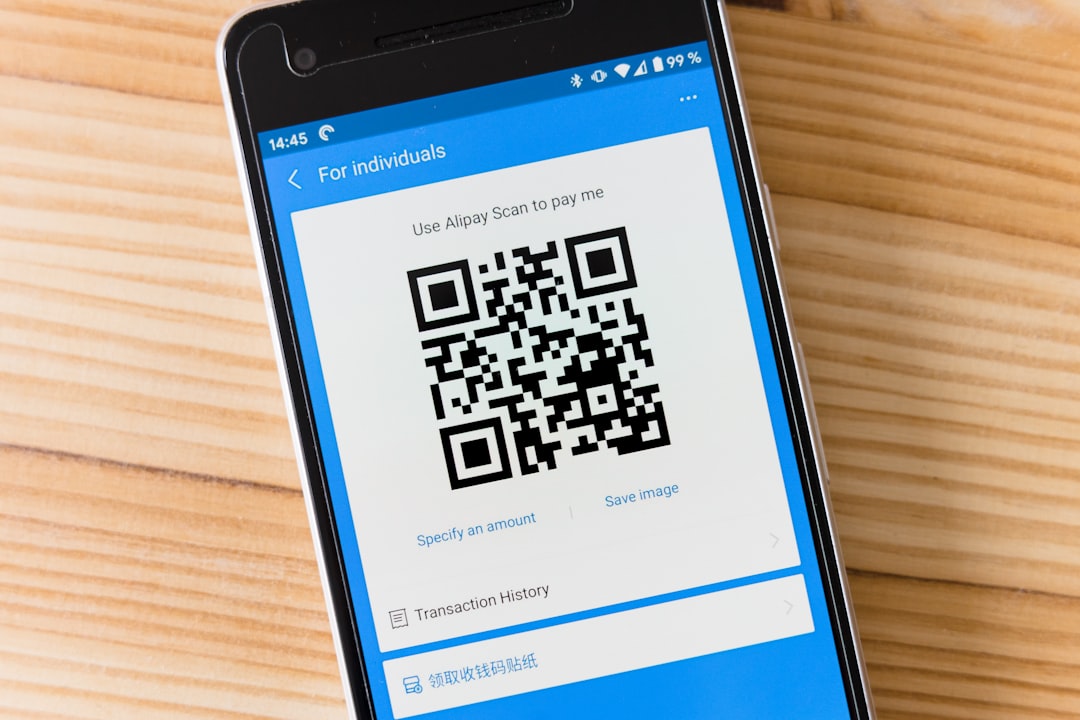
- The website displays a QR code.
- You scan the QR code with Twoku Authenticator.
- The app securely stores a secret key on your device.
- Twoku begins generating rotating six-digit codes every 30 seconds.
- During login, you enter both your password and the current code from the app.
The entire system works offline once set up. That means Twoku Authenticator does not require an internet connection to generate codes, reducing attack vectors significantly.
Key Benefits of Using Twoku Authenticator
1. Stronger Account Protection
The most obvious benefit is enhanced security. Even if your password is compromised in a data breach, attackers cannot access your account without physical access to your authentication device.
2. Protection Against Phishing
Phishing sites may steal your password, but they cannot use expired authentication codes. Because Twoku codes refresh frequently, the window of opportunity for attackers is extremely small.
3. Offline Code Generation
Unlike SMS-based verification, Twoku Authenticator does not rely on cellular service. SMS verification can be intercepted via SIM-swapping attacks, but app-generated codes remain secure within your device.
4. Multi-Account Support
You can connect Twoku Authenticator to multiple services, including:
- Email accounts
- Cloud storage platforms
- Cryptocurrency exchanges
- Social media networks
- Banking applications
This centralizes your security without complicating your login process.
5. Simple User Experience
Despite its advanced security mechanisms, Twoku Authenticator is incredibly user-friendly. Once configured, logging in requires only a quick glance at your device and entering a six-digit code.
Setting Up Twoku Authenticator: A Step-by-Step Guide
Getting started is straightforward. Follow these instructions:
Step 1: Download the App
Install Twoku Authenticator on your smartphone or tablet from your device’s app marketplace.
Step 2: Enable 2FA on Your Account
Log into the account you want to protect and navigate to Security Settings. Look for the option labeled Two-Factor Authentication or Authenticator App.
Step 3: Scan the QR Code
The website will generate a QR code. Open Twoku Authenticator and use its built-in scanner to capture the code.

Step 4: Confirm the Code
Enter the six-digit code generated by the app into the website’s verification box. Once confirmed, 2FA is activated.
That’s it. Your account now has significantly stronger protection.
Twoku Authenticator vs. SMS Authentication
Many platforms offer SMS-based verification. While better than nothing, SMS is less secure compared to authenticator apps.
- SMS codes can be intercepted through SIM swapping.
- Text messages travel through carrier networks, which may have vulnerabilities.
- SMS may fail in areas with poor signal.
Twoku Authenticator avoids these problems because it generates codes locally on your device. No messages are transmitted during code creation, significantly reducing exposure.
Best Practices for Maximum Security
Using Twoku Authenticator is an excellent step, but combining it with other best practices strengthens your security even further:
- Use unique passwords for every account.
- Enable 2FA everywhere it’s available.
- Secure your phone with biometric or PIN protection.
- Store backup recovery codes in a safe offline location.
- Regularly update your software to patch vulnerabilities.
Security works best when layered. Twoku Authenticator is a powerful tool, but combining it with smart digital habits creates nearly impenetrable defenses.
What Happens If You Lose Your Device?
One common concern about authenticator apps is device loss. Fortunately, most platforms provide recovery options when activating 2FA. These may include:
- Printable backup codes
- Secondary authentication methods
- Identity verification processes
It is crucial to save your backup codes during setup. Store them in a secure physical location, such as a locked drawer or safe.
If you upgrade to a new phone, you can typically transfer accounts by re-scanning QR codes or using built-in export features, depending on the service.
Common Myths About Authenticator Apps
“It’s Too Complicated”
In reality, setup takes only a few minutes. Daily use adds just seconds to your login time.
“Hackers Can Still Break In”
While no system is 100% invulnerable, using 2FA reduces unauthorized access risk dramatically. Most automated attacks target password-only accounts.
“It Slows Me Down”
The brief extra step during login is negligible compared to the potential damage of a hacked account.
Real-World Scenarios Where Twoku Authenticator Makes a Difference
Imagine receiving a notification that someone attempted to log into your email from another country. Without 2FA, that login might succeed if your password had been leaked. With Twoku Authenticator enabled, the attempt fails because the attacker lacks the time-sensitive code.

In another example, cryptocurrency investors often rely on authenticator apps to secure digital wallets. Given the irreversible nature of crypto transactions, that extra security layer can prevent catastrophic financial loss.
The Growing Importance of Two-Factor Authentication
As remote work expands and cloud-based platforms dominate both personal and professional environments, digital accounts serve as gateways to vast amounts of sensitive information. Email accounts reset passwords for other platforms. Cloud drives hold private documents. Social profiles influence reputations.
In this interconnected ecosystem, one compromised login can unravel multiple aspects of your digital life. Twoku Authenticator acts as a gatekeeper, ensuring that a stolen password alone is not enough to cause damage.
Final Thoughts: Is Twoku Authenticator Worth It?
Absolutely. In today’s threat landscape, relying on passwords alone is risky. Twoku Authenticator provides a simple yet highly effective safeguard against unauthorized access. It protects your accounts even if your password is exposed, prevents many phishing attempts from succeeding, and offers offline functionality for reliability.
Security doesn’t have to be complicated. Sometimes, small changes create the biggest impact. Enabling Twoku Authenticator may take only minutes, but it can save you from identity theft, financial loss, and countless hours of recovery effort.
Your online accounts deserve more than a password. Give them the protection they need.